In this Data Privacy and Protection in Finance Simulation, participants navigate the intricate landscape of evolving regulations, cybersecurity threats, and ethical dilemmas to safeguard sensitive customer data while enabling business innovation.
Core principles of data privacy
Key global regulatory frameworks
Data classification and lifecycle management
Designing and implementing a Data Protection Impact Assessment
Incident response planning and breach notification procedures
Managing third-party vendor and data processor risks
Privacy by Design and Default principles in product development
The ethics of data use, profiling, and AI in finance
Cross-border data transfer mechanisms
Communicating privacy policies and managing customer data rights requests
In the simulation, participants will:
Analyze complex business proposals for privacy and compliance risks.
Design and execute a DPIA to identify and mitigate potential harms.
Allocate a limited budget across competing needs: security tools, staff training, audit processes, or technology upgrades.
Respond to a simulated data breach, managing the technical response, regulatory notifications, and customer communications.
Negotiate data processing agreements with third-party vendors.
Advise senior management and "the board" on privacy strategy, balancing risk with commercial opportunity.
Handle customer data subject requests and balance operational fulfillment with regulatory deadlines.
Understand the core requirements and enforcement powers of major data privacy regulations.
Apply Privacy by Design principles to a financial product or service.
Develop a structured process for conducting and documenting a DPIA.
Formulate a crisis communication plan for a data breach incident.
Evaluate and mitigate risks associated with third-party data processors and cross-border data flows.
Articulate the business case for robust data protection, linking it to trust, reputation, and competitive advantage.
Navigate the ethical trade-offs between data utility for innovation and individual privacy rights.
Build confidence in making high-stakes compliance decisions under uncertainty and time pressure.
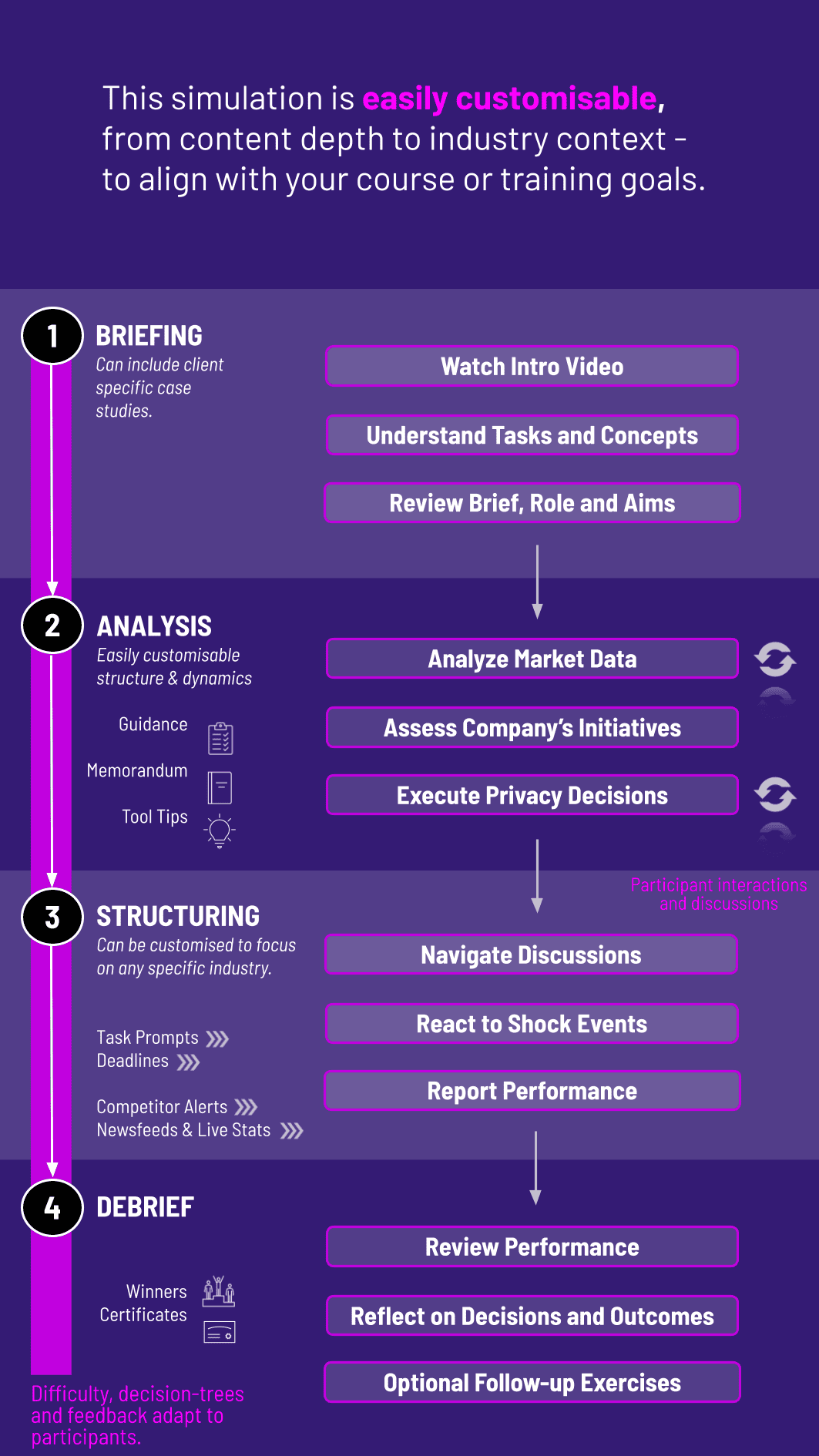
1. Receive a Scenario Brief Participants are introduced to a business initiative or an unfolding incident with significant privacy implications.
** 2. Analyze the Situation** They review relevant regulations, internal policies, system architectures, and stakeholder interests.
3. Make Strategic Decisions Participants choose how to proceed: approve, modify, or halt the initiative; allocate resources; draft key documents; and plan communications.
4. Collaborate Across Roles Teams may represent different functions (Legal, IT Security, Marketing, Product Development) to negotiate a unified strategy.
5. Communicate Outcomes Participants present their action plan to "regulators," deliver a board briefing, or draft a customer notification.
6. Review and Reflect Feedback highlights the compliance effectiveness, risk exposure, financial impact, and reputation score of their decisions. Strategies evolve across multiple rounds as scenarios escalate in complexity.
Who is this data privacy simulation designed for? It's ideal for students and professionals in finance, compliance, risk management, cybersecurity, legal studies, and business management who need to understand the practical application of data privacy laws.
Do I need prior legal or compliance experience? No prior experience is required. The simulation includes foundational instructional content on key regulations and concepts, making it accessible to all levels.
How long does the data privacy simulation run? Typically 3-4 hours, though it can be delivered in shorter modules (e.g., focused on breach response) or extended into a multi-session workshop.
Is the simulation individual or team-based? It supports both formats. The team-based format is highly recommended as it replicates the cross-functional collaboration essential in real-world privacy offices.
What regulations are covered? The simulation's core framework is based on GDPR principles, but it incorporates elements from CCPA and other major regimes, emphasizing a principles-based approach applicable in many jurisdictions.
Are real-world case studies used? Yes. Scenarios are inspired by real privacy incidents and regulatory actions within the financial services industry to ensure high relevance and realism.
Can instructors customize the simulation? Absolutely. Scenario focus (e.g., emphasis on marketing vs. fintech), regulatory jurisdiction, and organizational context can be tailored to specific audiences.
What roles does this simulation prepare participants for? It prepares participants for roles such as Data Protection Officer, Privacy Analyst, Compliance Manager, Information Security Consultant, and Risk Officer within the financial sector and beyond.
Accuracy and completeness of regulatory analysis and DPIA documentation.
Effectiveness of decisions in mitigating risk while supporting business objectives.
Quality and clarity of stakeholder communications.
Collaboration and adaptability in responding to new information and team input.
Ethical reasoning applied to dilemmas involving data use.
Join this 20-minute webinar, followed by a Q&A session, to immerse yourself in the simulation.
or
Book a 15-minute Zoom demo with one of our experts to explore how the simulation can benefit you.